Most cyberattacks are fairly mundane. In the worst cases, the user sees an on-screen ransom demand explaining that the computer is encrypted and can be unlocked after payment. Oftentimes, however, nothing visible happens at all — many types of malware act as surreptitiously as possible to maximize data theft before being spotted.
But with some cyberattacks, their scale or sophistication cannot fail to attract attention. This post is dedicated to the five most spectacular and notorious cyberattacks of the last decade.
WannaCry: A real epidemic
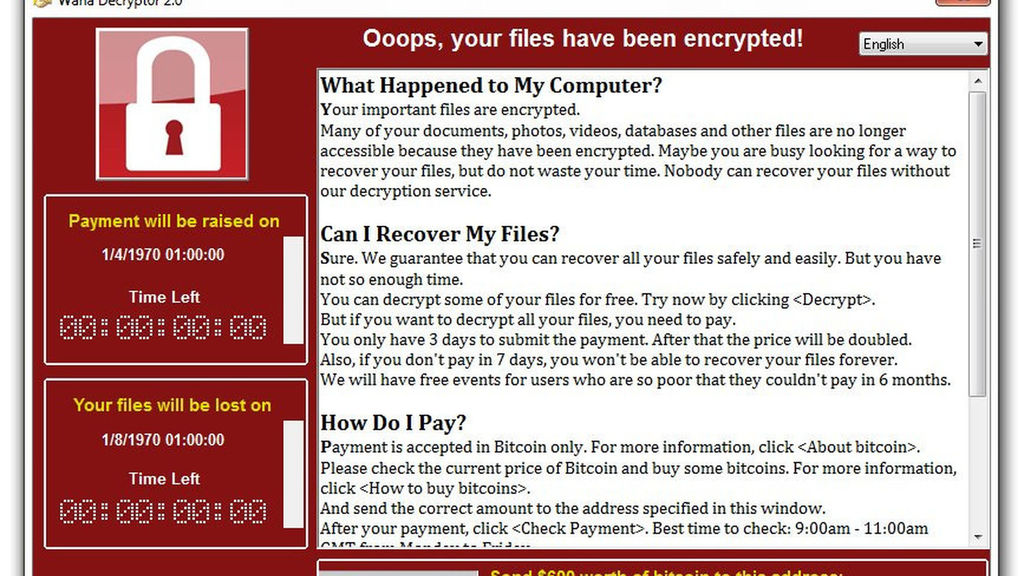
The WannaCry attack place ransomware, and laptop malware generally, on everyone’s map, even those that don’t apprehend a computer memory unit from a bite. exploitation exploits from the Equation cluster hacking team that were createdpublicallyon the market by the Shadow Brokers, the attackers created a monstrosity — a ransomware encryptor ready tounfold quickly over the weband native networks.
The four-day WannaCry epidemic knocked out quitetwo hundred,computers in one hundred fifty countries. This enclosedcrucial infrastructure: In some hospitals, WannaCry encrypted all devices, as well as medical instrumentation, and a few factories were forced to prevent production. Among recent attacks, WannaCry is that the most comprehensive.
See here for a lot of details concerning WannaCry, and here and here for business aspects of the epidemic. Incidentally, WannaCry continues to be out there, endangering the world’s computers. to search out out the way toset up Windows to remain protected, scan this post.
NotPetya/ExPetr: The costliest cyberattack to date
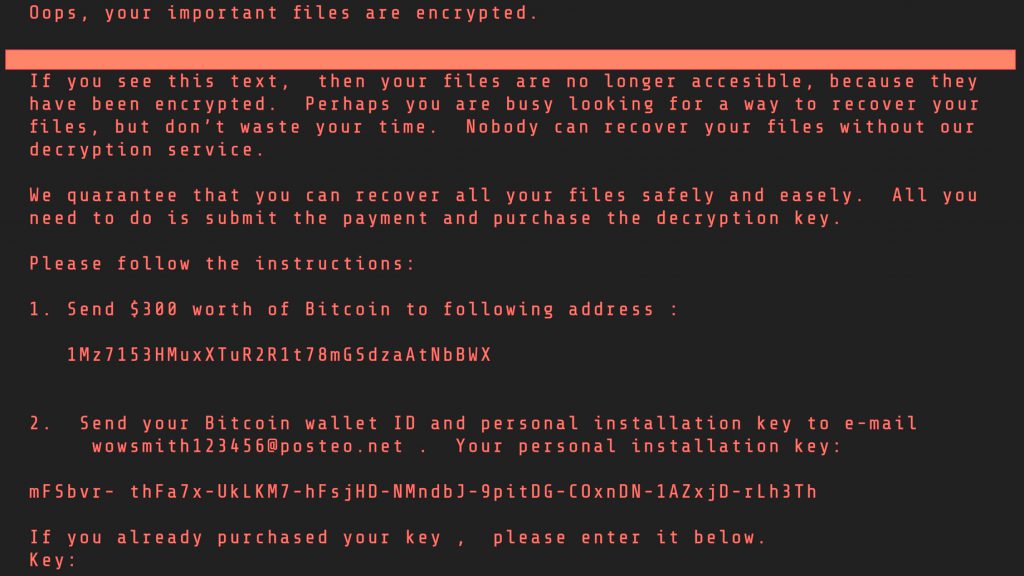
That said, the title of costliest epidemic doesn’tmove to WannaCry, however rather to a different ransomware encryptor (technically a wiper, however that doesn’t alter the lowest line) known as ExPetr, additionallyreferred to as NotPetya. Its operational principle was the same: victimisation EternalBlue and EtrernalRomance exploits, the worm emotionalround the net, irreversibly encrypting everything in its path.
Although it had been smaller in terms of total variety of infected machines, the NotPetya epidemic targeted in the main businesses, partiallyas a result ofone in all the initial propagation vectors was through the monetarycomputer codeMedoc. The cybercriminals managed to realizemanagement over the Medoc update server, inflictingmany purchasersvictimisation the computer code to receive the malware disguised as associate update, that then unfold across the network.
The injury from the NotPetya cyberattack is calculable at $10 billion, whereas WannaCry, consistent withvaried estimates, lies within the $4–$8 billion vary. NotPetya is taken into accountthe most costlyinternational cyberattack in history. Fingers crossed that if this record is ever broken, it won’t be before long.
More dataregarding the NotPetya/ExPetr epidemic is found during this post; the pain it caused businesses is examined here; and see here for why the epidemic, capable of disabling giant businesses, affects not solely those whose computers ar infected, however everybody else also.
Stuxnet: A smoking cybergun
Probably the most famous attack was the complex, multifaceted malware that disabled uranium-enrichment centrifuges in Iran, slowing down the country’s nuclear program for several years. It was Stuxnet that first prompted talk of the use of cyberweapons against industrial systems.
Back then, nothing could match Stuxnet for complexity or cunning — the worm was able to spread imperceptibly through USB flash drives, penetrating even computers that were not connected to the Internet or a local network.
The worm spun out of control and quickly proliferated around the world, infecting hundreds of thousands of computers. But it could not damage those computers; it had been created for a very specific task. The worm manifested itself only on computers operated by Siemens programmable controllers and software. On landing on such a machine, it reprogrammed these controllers. Then, by setting the rotational speed of the uranium-enrichment centrifuges too high, it physically destroyed them.
A lot of ink has been spilled over Stuxnet, including a whole book, but for a general understanding of how the worm spread and what it infected, this post should suffice.
DarkHotel: Spies in suite rooms
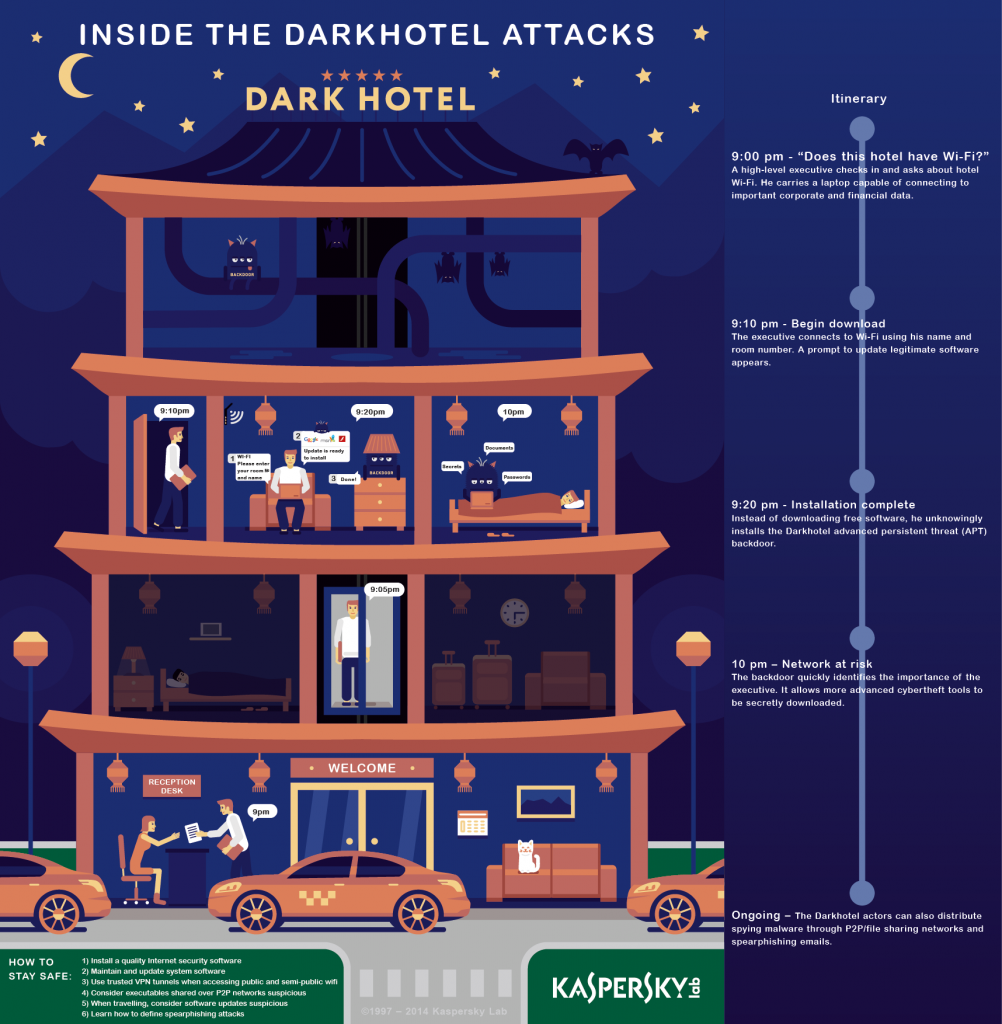
It is no secret that public Wi-Fi networks in cafés or airports don’t seem to bethe foremost secure. neverthelessseveral believe that in hotels things ought to be higher. albeit a hotel’s network is public, a minimum of some reasonably authorization is needed.
Such misconceptions have valuenumerousprime managers and high-levelofficers dearly. On connecting to a building network, they were prompted to put in a on the face of it legitimate update for a well-liked piece of software package, and instantly their devices were infected with the DarkHotel spyware, that the attackers specifically introduced into the network a number of days before their arrival and removed a number of days when. The sneaky spyware logged keystrokes and allowed the cybercriminals to conduct targeted phishing attacks.
Mirai: The fall of the Internet
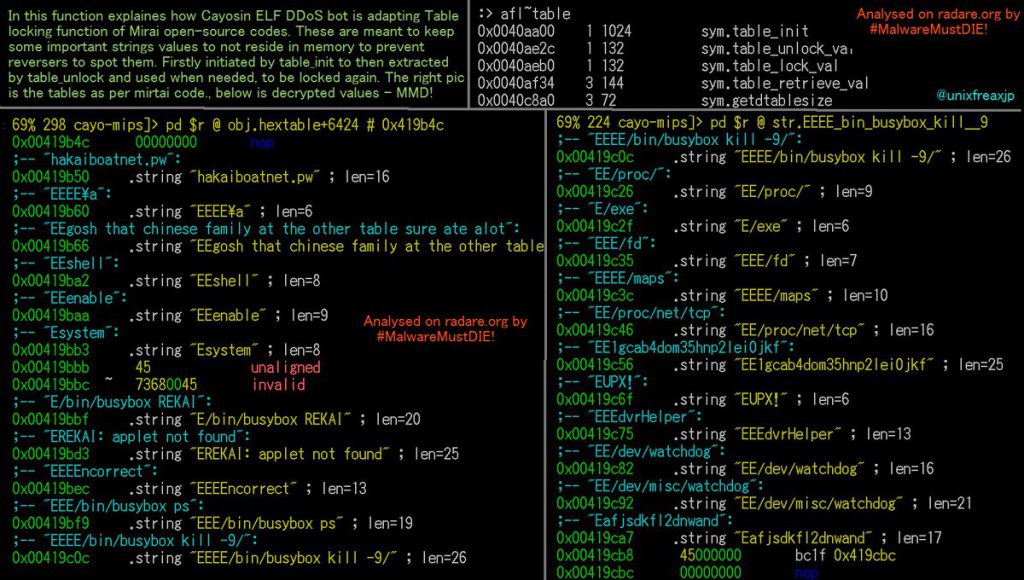
Botnets had been around for ages already, but the emergence of the Internet of Things really breathed new life into them. Devices whose security had never been considered and for which no antiviruses existed suddenly began to be infected on a massive scale. These devices then tracked down others of the same kind, and promptly passed on the contagion. This zombie armada, built on a piece of malware romantically named Mirai (translated from Japanese as “future”), grew and grew, all the while waiting for instructions.
Then one day — October 21, 2016 — the owners of this giant botnet decided to test its capabilities by causing its millions of digital video recorders, routers, IP cameras, and other “smart” equipment to flood the DNS service provider Dyn with requests.
Dyn simply could not withstand such a massive DDoS attack. The DNS, as well as services that relied on it, became unavailable: PayPal, Twitter, Netflix, Spotify, PlayStation online services, and many others in the US were affected. Dyn eventually recovered, but the sheer scale of the Mirai attack made the world sit up and think about the security of “smart” things — it was the mother of all wake-up calls.

